Trellix and Network Visibility
Scalable Threat Prevention
Your business relies on reliable connection to the Internet, but with today’s complex threat landscape, access isn’t as simple as it should be. Trellix’s Threat Prevention Platform stops cyber-attacks that traditional and next- generation firewalls, Intrusion Prevention Systems (IPS), anti-virus, and web gateways may miss.
Enable Threat Prevention
Trellix’s Threat Prevention Platform Protects Against Zero-Day Web Exploits and Multi-Protocol Callbacks.
Combining the platform with Keysight’s VisionOne creates a scalable and fault-tolerant solution that lets businesses maintain security and performance while meeting increasing demand.
• Easily scale deployments while lowering TCO
• Protects against zero-day, advanced targeted attacks
• Cuts off outbound malware transmissions across multiple protocols
• Integrates with EX Series to stop blended attacks
• Add a PX series appliance for network forensics capabilities and accelerated actionable insight.
Trellix: Real-Time IT Performance and Network Traffic Analytics
Trellix’s NX and Network Threat Prevention Platform appliances deliver a turnkey system that can be deployed inline at Internet egress points to block inbound exploits and outbound multi-protocol callbacks. Highlights include:
• Employing patented Multi-Vector Execution (MVX) to accurately confirm zero-day attacks, create real-time protections, and capture dynamic callback destinations
• Dynamic analysis of zero-day attacks within a full-featured virtual analysis environment yields realtime malware security content to protect the local network and share with subscribers of the Trellix Dynamic Threat Intelligence (DTI) cloud
• Signaling to incident response mechanisms such as SIEM
• TCP resets for out-of-band blocking of TCP, UDP, or HTTP connections
• Keysight’s VisionOne prevents overburdening of tools
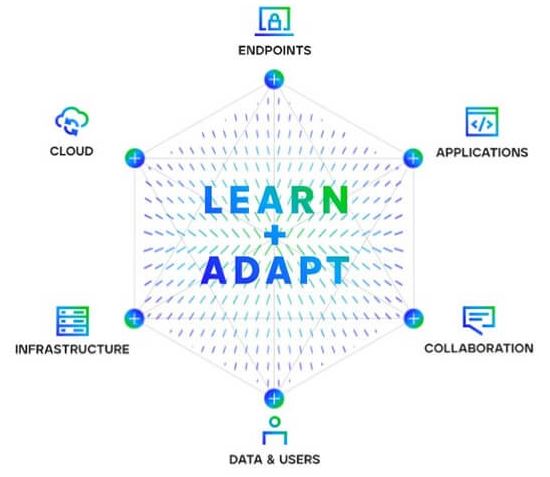
Edge to Core Visibility is Key
Trellix Solutions Use Deep Packet Inspection (DPI) to Understand and Identify Evidence of a Network Attack or Data Exfiltration.
The Keysight visibility platform uses a powerful processing and filtering engine inside its NPBs to strip away unnecessary data and isolate the packets that require security inspection. Pre-processing significantly reduces the load on monitoring tools and can reduce the need to add capacity. The NPBs can also decrypt secure packets for faster processing, eliminating the need for a separate decryption device.
Watch the video
Inline Visibility with Industry Leading Fast Failover
VisionOne is built specifically to prevent overburdening by distributing traffic to multiple monitoring tools. This allows deployments to scale with demand while maintaining security. Tool health is monitored using Heartbeat packets, allowing traffic to be proactively redirected to available or spare tools in case of failure.
VisionOne works with Trellix NX Appliances and AFO Bypass Switches (OEMed from Keysight) to optimize inline deployment. Bypass switches feature advanced Heartbeat and Link Fault Detect capabilities allow monitoring of Keysight’s xBalancer’s state information.
Three Switches send heartbeat packets to VisionOne to identify link anomalies and power failures.


